The future of cloud data Security – CloudAshur is the perfect solution for anyone wanting to securely store, share, manage and monitor data in the cloud. cloudAshur eliminates the security vulnerabilities
that exists with cloud platforms, such as lack of control and unauthorised access. Hackers and vulnerable users. Human error is also prevalent amongs data leakage incidents.
The consequences of a cloud account being hacked can bring about theft and leakage of confidential data, leading to potential job losses, adverse publicity, hefty fines and downfall of business.
ENCRYPT
to ensure the ultimate protection of your data stored in the cloud or on your local PC/MAC or any data storage device
SHARE
Your encrypted data security with authorised users in the cloud as well as email and file transfer services in real-time.
MANAGE
and monitor your cloudAshur device centrally
On-device Crypto-chip
Offering 100% real-time military grade AES-XTS or AES-ECB 256-bit Hardware Encryption with FIPS PUB 197 certified USB 3.0 encryption controller.
Uniquely incorporates Common Criteria EAL4+ ready secure microprocessor
Which offers ultimate security against hackers, detecting and responding to tampering with features such as:
– Dedicated hardware for protection against SPA/DPA/SEMA, DEMA attacks – Advanced protection against physical attacks, including Active Shield, Enhance Protection Object, CStack checker, Slope Detector and Parity Errors – Environmental Protection Systems protecting against voltage monitor, frequency monitor, temperature monitor and light protection – Secure Memory Management/Access Protection
Five Factor authentication
Something you have
- The cloudAshur hardware security module
Something you know
- 7-15 digit Admin/User configurable PIN
- Username and password for the iStorage cloudAshur Windows or macOS client app
- Where the data is stored, which cloud provider
- Username and password for the cloud account
- Username and password for the cloud account.Intelligently programmed to protect against all forms of brute force attacks.If the Admin PIN is entered incorrectly 10 consecutive times, all PINs and the encrypted encryption key will be lost forever.
Red – standby state
Green – User mode
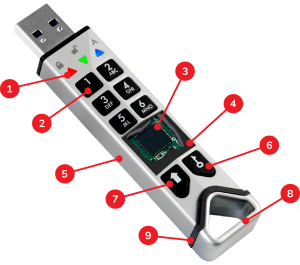
Blue – Admin mode
2. Polymer coated, wear resistant, alphanumeric keypad
3. Common Criteria EAL4+ ready secure microprocessor
4. Epoxy coating
5. Hard anodized and ruggedized extruded aluminium housing
6. Key button
7. SHIFT button
8. Zinc alloy (can be attached to keyring)
9. Rubber gasket
Making the module waterproof when sleeve is fitted
FIPS Level 3 compliant tamper proof & evident design
All critical components within the cloudAshur enclosure are covered by a layer of super tough epoxy resin, which is virtually impossible to remove without causing permanent damage to the critical components.
If breached, the cloudAshur modules tamper evident design will provide visible evidence that tampering has occurred.
One-time User recovery PIN
The Admin can program the cloudAshur with a one-time recovery PIN. This is extremely useful in situations where a User has forgotten the PIN to authenticate the cloudAshur.
This feature allows the User to enter the Recovery PIN and configure a new User PIN.
User PIN enrolment
The Admin can set a restriction policy for the user PIN. This includes setting the minimum length of the PIN, as well as requiring the input of one or more ‘Special Character’ if needed.
The ‘Special Character’ functions as ‘SHIFT
+ digit’
Whitelisting on networks
Configured with a unique VID/PID and internal/external serial number with barcode, allowing easy integration into standard end-point management software (white-listing), to meet internal corporate requirements


