SafeConsole
SafeConsole
Instantly gain complete and granular control
over all of your encrypted USB flash drives and portable hard drives
with the SafeConsole central management server software:
- Achieve compliance for USB storage usage, with full control and audit.
- Keep the productivity benefits of USB storage devices – without the risks of malware, data leaks and breaches.
Available as an on-premise software or as a DataLocker hosted cloud service with worldwide locations.
Control
Enforce policies such as password rules, file-type restrictions or geographic boundaries. Reset passwords, switch endpoints into readonly mode, and even remotely wipe them in case of loss or theft.
Inventory
Monitor all your encrypted endpoints, including their location anywhere in the world. Integrate with Active Directory to track users, assigned devices and connected computers with ease.
Audit
See which files are saved to or deleted from your encrypted endpoints at any given moment. Use a complete audit trail by user, including connections, login failures, resets and loss reports.
Report
Centrally handle the state of the devices over the Internet, setting them as disabled or lost- even perform factory resets remotely. Disable a user in AD and their devices are automatically disabled.
A SafeConsoleReady secure USB drive can be managed by the SafeConsole central device management server software
3 Major Reasons to Choose SafeConsoleReady Devices
- Unsecure USB Drives Spread Malware.
SafeConsoleReady secure USB drives fight malware. Unsecure USB Drives are Dat
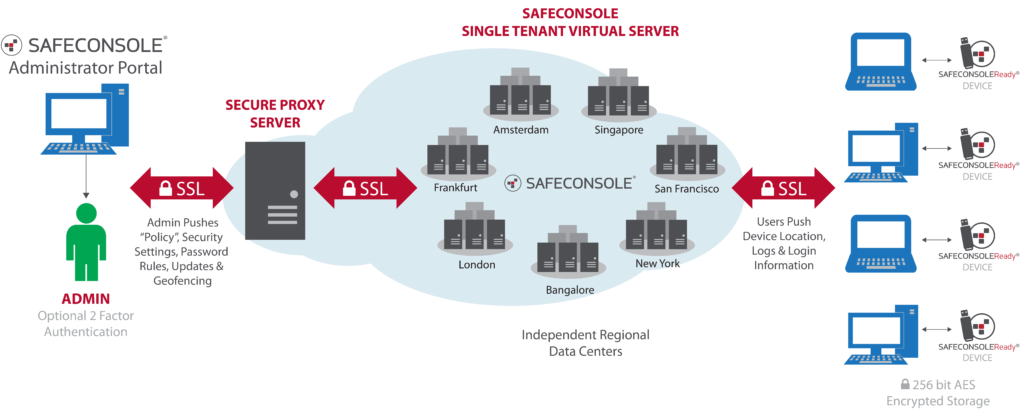
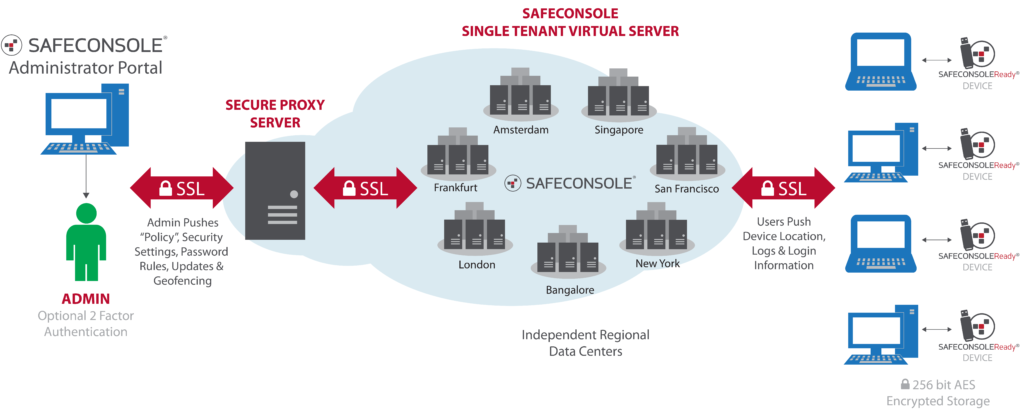
SafeConsole Deployment Options
SafeConsole Cloud – SaaS hosted by DataLocker world-wide
- Up and running in minutes
- No user content is stored on the cloud
- Your dedicated server can be hosted in your choice of cities around the globe
- Ideal for deployments of 1-500 endpoints
Why SafeConsole Cloud?
The SafeConsole Cloud (SCC) hosted service is the easiest and quickest way to get you organization managing and securing your encrypted endpoints.
- SCC is a single tenant solution. Your custom cloud hosted service is dedicated to only your organization.
- You can choose where to host your server, Amsterdam, Frankfurt, London, New York, San Francisco or Singapore to meet regulatory requirements.
- All network traffic is encrypted.
- Absolutely no client data is stored on the service.
PCI Compliance
For SafeConsole Cloud, our data centers have been certified by national and/or international security standards. Also, please note that SafeConsole Cloud is a single tenant solution, meaning that only your company’s service is hosted that specific virtual server. Also, no actual data from the storage products is saved on the cloud. Only SafeConsole, the management console, is hosted on the cloud.
- The New York facility is SSAE16 SOC-1 Type II certified.
- The Amsterdam facility is ISO27001:2005 and ISO9001 certified.
- The San Francisco facility is SSAE16 SOC-1 Type II certified.
- The Singapore facility is ISO27001:2005 certified.
- The London facility is ISO9001:2008, ISO27001, and SSAE16 / ISAE 3402 certified.
- The Frankfurt facility is ISO9001:2008, ISO27001:2005, and ISO22301:2012 certified.
- The Toronto facility will be SSAE16 SOC-1 and SOC-2 compliant in December, 2015.
SafeConsole On-Prem – installed on your own Windows server
SafeConsole On-Prem is easy to deploy if your organization requires an on-premise or hybrid cloud solution:
- Requires a dedicated Windows-based server
- Log in and manage from anywhere
- Administrators can authenticate to access SafeConsole with their AD credentials.
- Ideal for deployments of 300+ endpoints
Minimum Requirements
- Pentium Quad Core or higher class system
- 2GHz or faster CPU minimum
- Windows Server 2003, 2008, or 2012
- 4GB of free RAM
- 20GB of free hard disk space required
SafeConsoleReady Vendors
DataLocker offers a full range of SafeConsoleReady secure USB flash drives and encrypted hard drives.
 |
 |
 |
| DataLocker DL3 Encrypted External Hard Drive | Sentry 3 FIPS Encrypted Flash Drive | Sentry 3.0 Encrypted Flash Drive |
Kingston Digital
DataTraveler Vault Privacy 3.0 – FIPS197 – SKUs
DTVP30DM/4GB, DTVP30DM/8GB, DTVP30DM/16GB, DTVP30DM/32GB, DTVP30DM/64GB
DataTraveler 4000 G2 – FIPS 140-2 level 3 – SKUs
DT4000G2DM/4GB, DT4000G2DM/8GB, DT4000G2DM/16GB, DT4000G2DM/32GB, DT4000G2DM/64GB
Core Features of a SafeConsole Ready Device
SafeConsole 5 |
|
|---|---|
| US based datacenter | ⚫ |
| Private cloud server SaaS | ⚫ |
| World-wide cloud hosting options | ⚫ |
| Available as an On-Prem installation | Yes, Windows installable, automigrate from 4.7/4.9 |
| Compatible Devices | Cardwave SafeToGo, Kingston DTVP30DM, DT4000DM, DataLocker Sentry, DataLocker DL3 hard drives |
| Crossplatform Windows and select devices for Mac | ⚫ |
| Forced management available? | ⚫ |
| Browser based service interface | ⚫ |
| Automatic inventory directory of all users and devices | ⚫ |
| Self-service plug-and-play device deployment | ⚫ |
| Centrally enforce security policies of devices | ⚫ |
| Accessible from mobile device | ⚫ |
| Filter and sort data tables | ⚫ |
| Search for devices and users | ⚫ |
| Two-factor authentication to management system | Mobile text message or token |
| Deployment Wizard | ⚫ |
| Information Dashboard | ⚫ |
| Optimized for large enterprises | ⚫ |
| Admin and role management | ⚫ |
| Multiple administrator roles | ⚫ |
| Dynamic licensing | ⚫ |
| Integrated help text in the user interface | ⚫ |
| Export data in CSV format | ⚫ |
| Active directory integration | ⚫ |
| Automated server updates | ⚫ |
| Server/device locked to organization with a certificate | ⚫ |
| Custom device password policy | ⚫ |
| Device remote password reset over phone or Internet (Challenge/Response - PKI). | ⚫ |
| Local device self-service password reset (PKI) using ZoneBuilder. | ⚫ |
| ZoneBuilder (automatic unlock on trusted user accounts) | ⚫ |
| Remotely set device as disabled. | ⚫ |
| Remotely reset device. | ⚫ |
| Remotely set device as lost or to deny access to the device. | ⚫ |
| Remotely reassign device to new user | ⚫ |
| Manage the device states. Automate with rules. | ⚫ |
| Self-service mark a device as “found” on sucessful unlock. | ⚫ |
| Offline restrictions for device usage | ⚫ |
| Custom return-to-owner message displayed on device if lost. | ⚫ |
| File Restrictions (white-list accepted file-types) anti-malware | ⚫ |
| Inactivity Lock management | ⚫ |
| Device/User audit (Excel, XML) | ⚫ |
| File audit (Excel, XML, Syslog) | ⚫ |
| Audit reports | ⚫ |
| Backup | Integration available |
| Publisher file distribution | ⚫ |
| ZoneBuilder (restrict devices to work on select machines) | ⚫ |
| Autorun applications | ⚫ |
| Enable users to unlock drives in write protected mode | ⚫ |
| Collect and use device user information. Sort and search based on collected information in the Device Overview. | ⚫ |
| Customize device “about” screen | ⚫ |
| Manage portable antivirus on the devices | ESET |
| Geo location of devices | ⚫ |
| Geo fencing of devices | ⚫ |